Radiant Node Start 267-525-9887 signals a privacy-focused workflow for unlocking contact information. It emphasizes identity verification, data minimization, and auditable actions. The approach relies on consent and purpose limitation, with access tightly controlled and logged. Encryption protects data at rest and in transit. Stakeholders must balance transparency with security, ensuring lawful processing. The implications raise questions about ethical boundaries and practical safeguards, inviting closer scrutiny of how such signals influence verification and contact access.
What “Radiant Node Start 267-525-9887” Means in Context
The phrase “Radiant Node Start 267-525-9887” functions as a label that combines a branding element with a contact number, suggesting a starting point for an outreach or service workflow. In interpretation context, this label marks a functional cue rather than a literal instruction, guiding interpretation toward initiating a verification sequence while preserving user autonomy and freedom in approach.
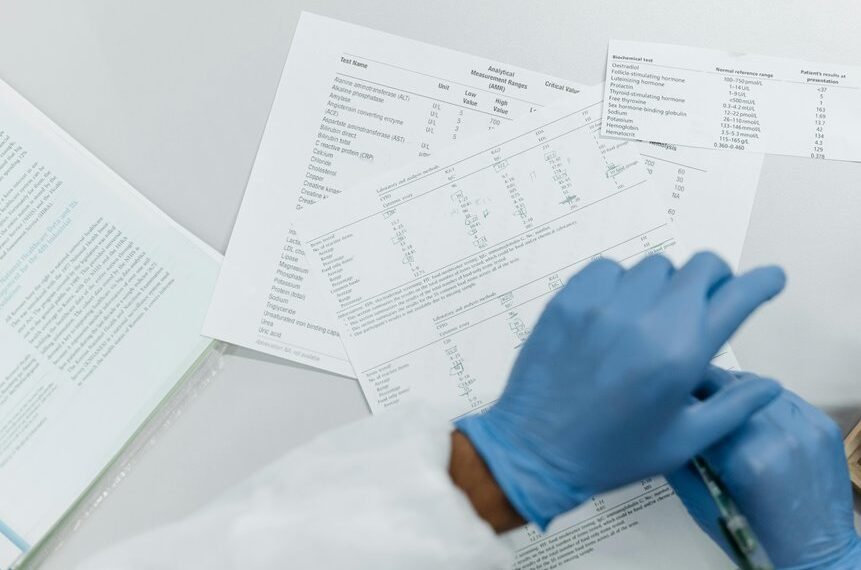
Step-by-Step Guide to Verifying Identity Before Unlocking Contacts
Before proceeding to unlock contacts, the process begins with a careful identity verification sequence that follows the preceding label’s focus on initiating outreach. The step-by-step method outlines verification processes, including authentication checks, document validation, and cross-referencing records. Emphasis rests on data minimization and ethical considerations, ensuring privacy while enabling access, and maintaining transparent, freedom-friendly procedures throughout the verification workflow.
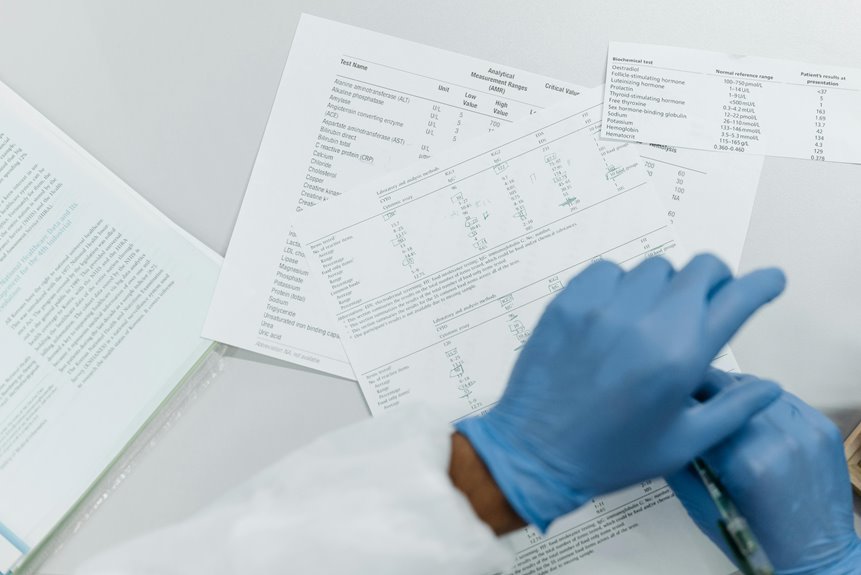
Best Practices for Accessing Contact Information Responsibly
Best practices for accessing contact information responsibly center on minimizing impacts to privacy while enabling legitimate outreach. The detached analysis emphasizes consent, purpose limitation, and transparent intent. Adherence supports privacy ethics and data security by restricting access, logging actions, and employing encryption. Practitioners document provenance, uphold auditability, and avoid intrusive scraping, ensuring respectful outreach that respects autonomy and safeguards individual trust.
Navigating Privacy Laws, Ethics, and Security Risks When Unlocking Contacts
Navigating privacy laws, ethics, and security risks when unlocking contacts requires a careful balance between legitimate outreach and fundamental rights.
The discussion emphasizes privacy compliance, ensuring lawful data collection and processing, while respecting user autonomy.
It highlights ethical considerations, informed consent, and transparency.
Security best practices, robust access controls, and data minimization reduce exposure, safeguarding participants without compromising essential freedom.
Conclusion
In the present discourse, the phrase Radiant Node Start 267-525-9887 signals a careful initiation rather than a reckless unveiling. The process implies measured steps, guarded access, and disciplined oversight, where privacy considerations are not merely decorative but foundational. Euphemistic assurances mask rigorous verification and ethical restraint, ensuring that contact details, when disclosed, arrive with consent and purpose. Ultimately, responsible stewardship, transparent governance, and continual risk awareness coalesce, guiding sensitive connections toward legitimate, trustful outcomes.