Radiant Nodes are positioned to support real-time, privacy-preserving contact tracing through cryptographic governance and secure proximity signals. They aim to balance rapid exposure analytics with limited data retention, emphasizing auditable change management and reproducible deployment. The approach highlights transparency and user autonomy while noting costs and operational ethics. This framing raises questions about governance, data minimization, and practical trade-offs that warrant further examination.
What Radiant Nodes Do and Why They Matter
Radiant Nodes function as the distributed infrastructure that underpins secure contact tracing networks, processing and routing signals while enforcing privacy-preserving constraints. They organize data flows with Radial symmetry, enabling uniform coverage and resilient routing. Cryptographic governance guides access, auditability, and key management, reducing risk exposure. This architecture supports scalable autonomy, empowering systems to balance freedom with accountability in public health infrastructure.
How Real-Time Contact Tracking Works in Practice
Real-time contact tracking operationalizes the exchange and analysis of proximity signals as they occur, leveraging Radiant Nodes to route data streams, apply privacy-preserving constraints, and update exposure metrics without compromising individual anonymity.
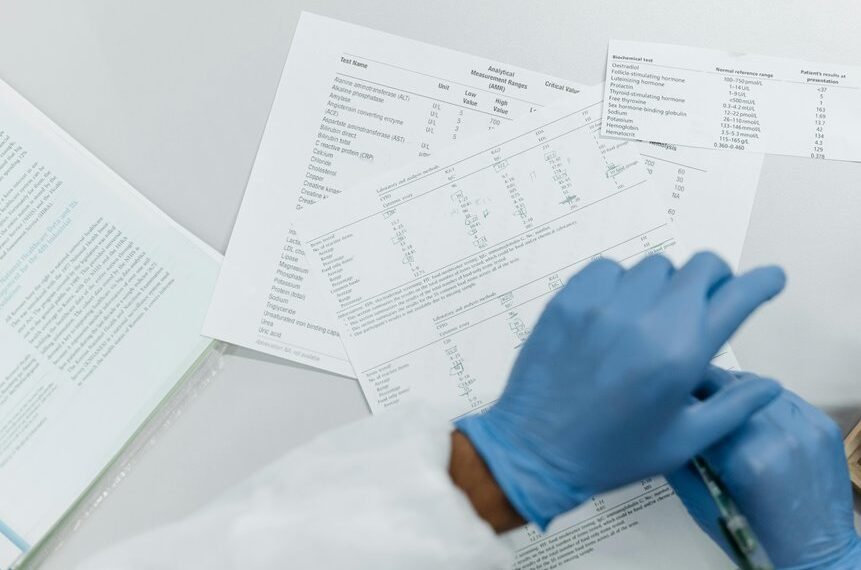
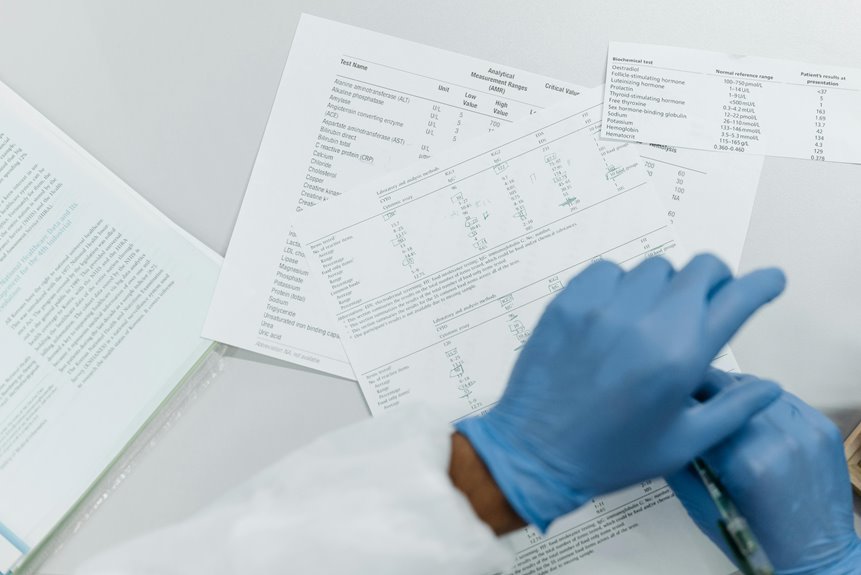
Data pipelines emphasize privacy preserving methods, centralized auditing, and minimal retention.
The approach balances data minimization with actionable insights, guiding tracing ethics while preserving user autonomy and transparent risk assessment.
Deploying Radiant Nodes: Steps, Costs, and Ethics
Deploying Radiant Nodes entails a structured sequence of installation, configuration, and governance tasks designed to maintain data integrity while controlling operational costs.
The process emphasizes reproducibility, fault tolerance, and auditable change management.
Costs arise from hardware, software licenses, and maintenance.
Privacy safeguards, data minimization, and ethical considerations guide deployment decisions, balancing transparency with performance and freedom to innovate.
Evaluating Trade-offs and Best Practices for Privacy-Respecting Tracing
What trade-offs arise when implementing privacy-respecting tracing, and how do they affect effectiveness, cost, and user trust? Privacy preserving approaches reduce data exposure but may lower signal fidelity, increasing false positives or delayed alerts. Data minimization lowers storage needs and risk, yet can constrain analytics. Balancing transparency, consent, and security supports freedom while maintaining reasonable efficacy and sustainable costs.
Conclusion
Radiant Nodes provide a privacy-conscious path for proximity sensing, balancing real-time analytics with user autonomy. The architecture enables auditable data flows, cryptographic governance, and minimal retention, supporting actionable insights without pervasive surveillance. While trade-offs exist—latency, setup costs, and governance overhead—the framework emphasizes transparency and reproducibility. In practice, this approach resembles a well-turnished genome map: precise, detailed, and capable of inference without exposing the whole organism. It is, therefore, a measured, ethics-forward evolution in contact tracing.