Stellar Gateway’s 385-297-8567 results offer a disciplined framework for contact discovery. The focus is on phone-name verification, privacy, and consent. It emphasizes minimal data, auditable processes, and clear governance. Practitioners are guided toward accurate, ethical outreach with documented justifications. The approach weighs risks and rewards, balancing efficiency with responsibility. The implications for trusted connections are substantial, but the path forward hinges on disciplined verification and transparent intent. There’s more to consider before acting.
What Is a Stellar Gateway Lookup and Why It Matters
A stellar gateway lookup is a targeted method for identifying and verifying contact points associated with a specific organization or individual, enabling precise outreach and risk assessment. The practice delivers clarity, enabling strategic decisions and protective autonomy. A stellar gateway fosters informed connections, while inspiring lookup elevates confidence in authenticity, reducing uncertainty and expanding freedom through deliberate, data-driven engagement.
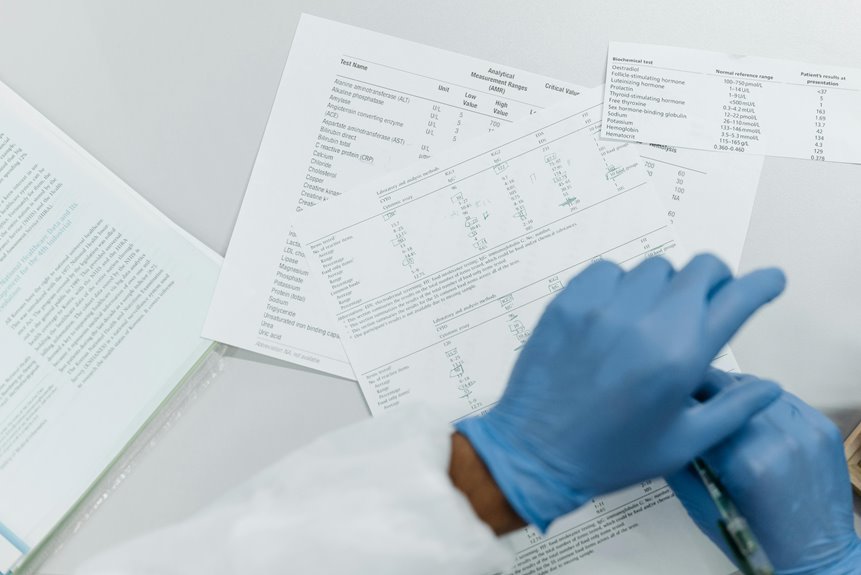
How to Verify a Phone-Name Match Safely and Ethically
Phone-name verification should be approached as a safeguards-driven process that confirms that a given phone number truly belongs to the stated contact. The approach emphasizes verify identity while respecting privacy, using ethical checks and documented consent first. Stakeholders weigh risks, transparency, and proportionality; actions are justified by necessity, avoiding coercion. Informed choices empower users while preserving freedom and trust.
Practical Steps for Conducting Inspiring Contact Lookups
Practical steps for conducting inspiring contact lookups require a disciplined, methodical approach that prioritizes accuracy, consent, and privacy. The process emphasizes verification, transparent intent, and ethical lookup practices, guiding researchers to collect minimal data while expanding access to legitimate networks. By maintaining accountability, organizations enable trustworthy outreach, sustain user autonomy, and promote responsible engagement that aligns with freedom-seeking audiences and ethical lookup standards.
Pitfalls, Privacy, and Best Practices for Responsible Use
What risks accompany responsible use, and how can organizations mitigate them without hindering legitimate outreach? The approach emphasizes privacy considerations, data minimization pitfalls, and ethical guidelines, promoting consent awareness. A strategic framework weighs transparency, proportionality, and accountability, enabling informed engagement while preserving freedom. Careful governance and auditable processes reduce misuse, balance innovation with rights, and sustain trust across ethically aligned outreach initiatives.
Conclusion
In the quiet orchard of outreach, the phone-number tether is a seed and the name a sun. Verification waters growth with candor, pruning the branches of misdirection. When intent is transparent, the soil remains fertile for trust; data becomes harvest, not hazard. A beacon shines not to entice, but to guide: responsible connections cultivate lasting roots. Yet vigilance is the wind, reminding every passerby that power without consent withers the grove. stewardship, then, is the true harvest.