Radiant Node integrates modular data collection with privacy-preserving analytics to support rapid risk assessment in proximity networks. The 323-421-5203 role centers on transparent consent, explicit approvals, and auditable logs to preserve user autonomy. Implementations emphasize encrypted communications, robust governance, and minimal data handling. This approach balances safety gains with privacy protections, yet practical deployments raise questions about governance, control, and accountability that demand careful scrutiny. The next considerations reveal where these safeguards truly stand.
What Is Radiant Node and Why It Powers Contact Tracking
Radiant Node refers to a distributed framework designed to optimize contact tracing by securely recording proximity events and enabling rapid, privacy-preserving data analysis.
It operates through modular components that coordinate data collection, anonymization, and efficient querying.
In practice, Radiant Node enables scalable Contact Tracking while maintaining standards for security, transparency, and user autonomy, ensuring responsible, evidence-based public health actions.
How 323-421-5203 Enables Transparent Consent in Tracking
The mechanism 323-421-5203, as part of the Radiant Node ecosystem, provides transparent consent by logging explicit user approvals for proximity data collection and usage.
This approach reinforces privacy safeguards and strengthens consent management, ensuring individuals retain control over their data.
The system emphasizes auditable records, minimal data retention, and clear disclosures, fostering informed participation while maintaining vigilant compliance with evolving privacy expectations.
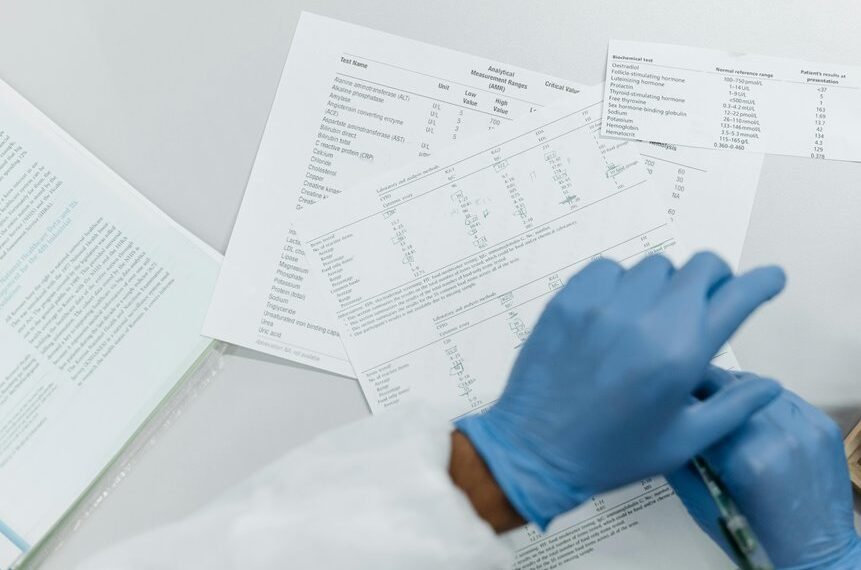
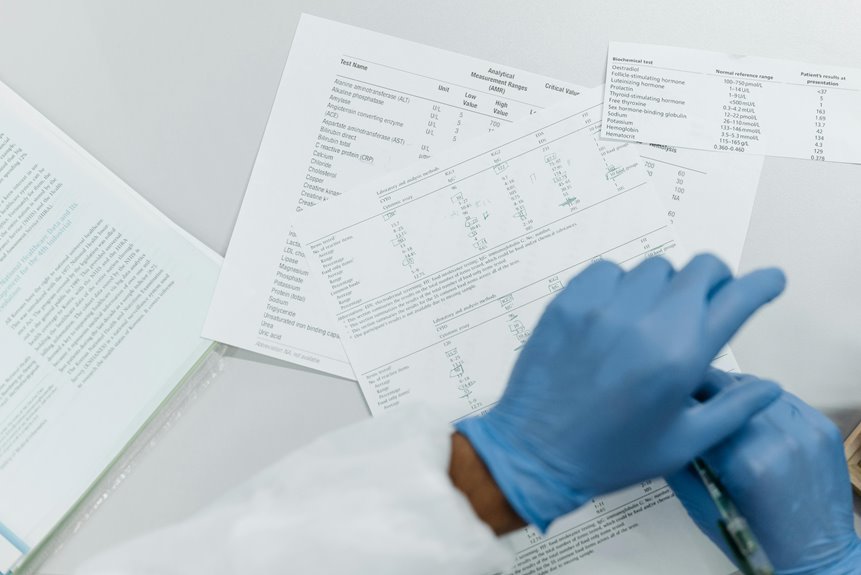
Practical Steps to Implement Radiant Node for Safe Contact Networks
To implement Radiant Node for safe contact networks, a structured, privacy-conscious deployment plan is essential. The approach emphasizes minimal data collection, transparent governance, and modular safeguards. Stakeholders map roles, enforce access controls, and audit logs. Technical steps include secure node setup and encrypted communications. Compliance reviews accompany testing, ensuring idea1 two word and idea2 two word remain protected and verifiably independent.
Driving Safety and Efficiency: Real-World Use Cases and Trade-offs
Driving safety and efficiency hinge on practical deployments that balance performance with privacy protections. Real-world use cases reveal operational gains from targeted data collection, traffic-aware routing, and autonomous diagnostics, yet expose trade-offs in scale, latency, and interoperability. Privacy compliance and data minimization remain core controls, guiding governance, audits, and user trust without compromising critical safety advancements. Vigilant implementation sustains freedom through accountable innovation.
Conclusion
In the quiet harbor of a crowded world, Radiant Node stands as a lighthouse, guiding ships of data away from perilous shoals. The 323-421-5203 beacon acts like a trusted harbor master, demanding consent before passage and recording every clear signal. As tides of proximity rise, the system tampers fear with transparency, encrypts the cargo, and audits every lantern glow. A vigilant guardian keeps the voyage safe, allowing communities to sail with both speed and dignity.