The velocity flow for 216-202-8306 frames a secure contact lookup as a real-time, privacy-preserving process. It integrates rapid verification with deterministic outcomes, balancing speed and accuracy. The approach emphasizes modular, low-latency components and auditable trails to maintain data integrity and consent. This foundation invites examination of architecture and governance, leaving questions about integration and safeguards that warrant further attention.
What Is Secure Contact Lookup and Why It Matters
Secure contact lookup refers to the process of determining and confirming an individual’s contact information from trusted sources while safeguarding privacy and data integrity. It enables organizations to verify identities without exposing personal data. A robust approach supports secure lookup, ensuring accuracy and consent. In real time, verified details reduce risk, accelerate communications, and empower users to control how their information is shared and used.
Designing Velocity-Validated Lookups for Real Time Security
Velocity-validated lookups for real-time security require a design that balances speed with accuracy. The approach emphasizes modular, low-latency components that enable secure lookup operations without compromising throughput. Real time validation relies on compact data structures and streaming checks, ensuring consistency under load. Architectural choices prioritize resilience, observable metrics, and deterministic outcomes, supporting confident decision-making within freedom-focused, agile environments.
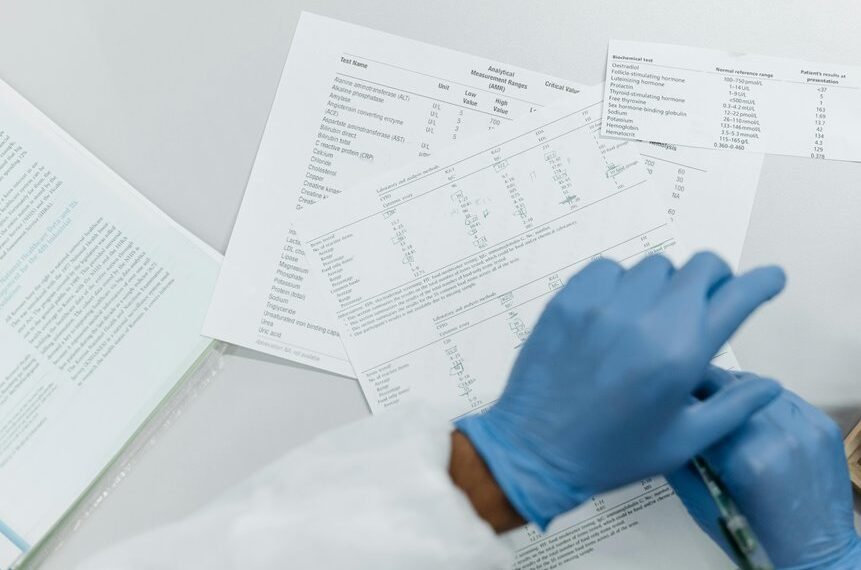
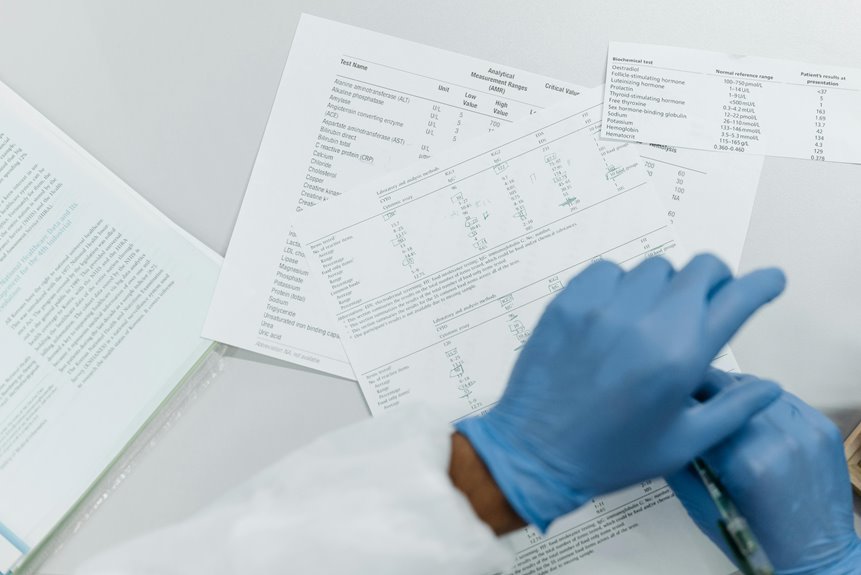
Practical Architecture and Best Practices for 360° Protection
Practical architecture for 360° protection integrates layered defenses, continuous monitoring, and rapid threat containment to deliver comprehensive security coverage. The approach emphasizes modular controls, secure authentication, and automated incident response, reducing attack surfaces. Real time validation shields identity and transactions while policy-driven access governs permissions. Independent verification, auditable logs, and resilient recovery ensure persistent protection with freedom to operate securely.
Measuring Success: Metrics, Trade-offs, and Next Steps
How can organizations quantify the effectiveness of their security posture and balance competing objectives? The discussion centers on measurable outcomes, trade-offs, and iterative refinement. Security metrics guide decision-making while acknowledging data privacy and latency issues. Clear baselines, dashboards, and governance enable disciplined evaluation. Next steps emphasize incremental improvements, risk-aware prioritization, and transparent communication to sustain freedom through robust protection.
Conclusion
Velocity-supported contact lookup delivers speed with safeguards, speed with consent, speed with accuracy. It emphasizes real-time verification, real-time privacy, real-time audibility, real-time integrity. It combines modular components, deterministic outcomes, and auditable processes, enabling rapid action without exposing private data. It ensures trusted sources, trusted verification, trusted transactions, trusted communications. It creates confidence, creates compliance, creates resilience, creates clarity. It demonstrates that speed and security are not adversaries but partners, partners in protection, partners in performance.